It’s another week and there’s another now-more-often Weekly Threat Report. We’ll cover:
- A ransomware group that has seemingly grown a conscience
- A sudo vulnerability you may need to update
- A recent Google Chrome update that has caused quite the stir
Read on.
Ransomware operators with a conscience
Last week, we talked about the death of Emotet after a team of law enforcement agencies from around the world took over Emotet C2 servers and arrested multiple individuals. At the end of last week (January 30), the threat actors behind FonixCrypter Ransomware gave in to their conscience and voluntarily halted operations.
In a statement released on Twitter, the FonixCrypter group claims to have “come to the conclusion we should use our abilities in positive ways and help others.” They then followed up the announcement by releasing the master decryption key and a decryption tool that could be used to decrypt all those affected by FonixCrypter.
Perch Labs and other research groups have reviewed the decrypter tool, and everything seems legit. There do not appear to be any backdoors or hidden functionality in the tool as some paranoid researchers (this author, for example) originally believed.
The decrypter tool is allegedly the same tool used by the Fonix group to decrypt individual files as proof decryption works during the negotiation process. As such, the tool works fine for decrypting one file at a time but isn’t very useful for decrypting an entire infected system. The important thing is that the master key works, and other decrypter tools can be written using this key.
Currently, Emsisoft is adding this capability to their free ransomware decryption tools. We recommend waiting for this tool to be updated rather than using the one the Fonix group released. Even though no one has found anything hidden in this tool, I always recommend paranoia as a legitimate strategy when it comes to ransomware.
As Joseph Heller said in Catch-22, “Just because you’re paranoid doesn’t mean they aren’t after you.”
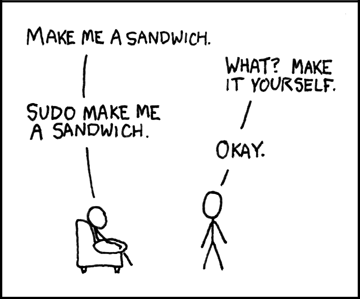
Sudo privilege escalation vulnerability
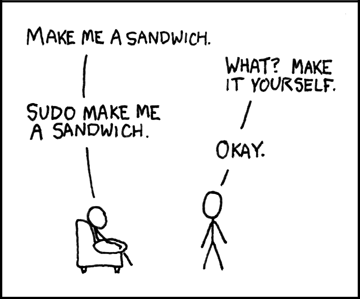
Source: xkcd (there’s one for everything, right?)
Last week, the Qualys Research Team discovered a heap overflow vulnerability in sudo. Sudo is a Linux command that allows a user to execute another command with higher privileges, most commonly used to do something as the superuser root (SuperUser DO = sudo).
It can be configured per user/group so a user can perform one specific task, such as calling mount to load a flash drive (usually done with SUID, but that’s a completely different topic), or can allow a user to execute all commands as root or any other user.
However, the recently disclosed vulnerability – which has been hiding in the source code since July 2011 – will allow anyone who already has access to a system to gain full root access.
Qualys’ original disclosure was carefully coordinated with the authors of sudo and major Linux distributions so that patches resolving this issue have already been made available. That being said, it has come to light this week that the latest version of macOS (Big Sur) is also vulnerable, and as of right now, there hasn’t yet been a patch released by Apple.
We recommend keeping up to date with your security patches as standard operating procedure but want to doubly recommend that you patch your systems. Qualys did not initially release a proof-of-concept, but several researchers have duplicated their work over the past week, and there are now several available for testing.
You can check for the vulnerability simply and safely by running the following command:
sudoedit -s '\' `perl -e 'print "A" x 65536'`
If the above command crashes with a core dump, then you are currently running a vulnerable version of sudo and should update to the latest version ASAP.
Perch systems, including your Perch sensors, were patched on the day the vulnerability was disclosed.
Google patch, or backdoor?
Supply chain attacks have been at the top of everyone’s mind in 2021 after the major SolarWinds compromise that has been at the top of the news since Mid-December. In this climate, a recent Google Chrome update has caused a bit of a stir.
On Tuesday, February 2, Google released Google Chrome 88.0.4324.146, a minor version upgrade that includes 6 security fixes: 1 critical, 4 high, and one medium. As soon as it was released, reports started coming in that this version of Chrome was being detected by Microsoft Defender Advanced Threat Protection (ATP), the commercial version of Microsoft Defender, as a generic backdoor trojan named “PHP/Funvalget.A.”
A discussion broke out on VirusTotal and Twitter as sysadmins worldwide wanted to know if this was a false positive or another major supply chain attack. The IT world held its collective breath for about an hour, waiting for confirmation from Google or Microsoft that this was indeed a false positive and the events of last year weren’t about to repeat. At the time of this writing, official word has not yet been released, though one user on VirusTotal claims Microsoft has acknowledged this as a false positive.
By the way, did you know that Perch has a Microsoft Defender ATP integration? If you’re a Perch customer using ATP, enable log ingestion today by following the instructions at https://perch.help/integrations/security/msft-defender/.
That’s all for this week. Check back in next week for another round of updates.
- Bryson Medlock, The Dungeon Master
References:
https://www.zdnet.com/article/fonixcrypter-ransomware-gang-releases-master-decryption-key/
https://twitter.com/fnx67482837/status/1355255873581539333
https://www.bleepingcomputer.com/news/security/fonix-ransomware-shuts-down-and-releases-master-decryption-key/
https://www.zdnet.com/article/recent-root-giving-sudo-bug-also-impacts-macos
https://blog.qualys.com/vulnerabilities-research/2021/01/26/cve-2021-3156-heap-based-buffer-overflow-in-sudo-baron-samedit
https://www.zdnet.com/article/microsoft-defender-atp-is-detecting-yesterdays-chrome-update-as-a-backdoor/