An evasive new strain of malware dramatically burst into the sunlight last week. Here’s what you need to know:
- SolarWinds Orion business software was trojaned with malware referred to as SunBurst.
- The campaign was widespread and impacted thousands of organizations around the world.
- Perch deployed signatures to detect SunBurst activity within 24 hours of the initial report.
- Perch reviewed the last 90 days of data for all customers for SunBurst-related activity. We’ve notified all customers showing signs of infection.
- Perch doesn’t use any SolarWinds products.
SunBurst
On December 13, 2020, FireEye released a report detailing the discovery of SunBurst malware. FireEye discovered the malware while investigating their own breach where an arsenal of exploits was stolen. Because of that, we’ll need to watch out for these tools now attacking us.
Luckily, FireEye released some signatures to detect their own tools in action. This is like the NSA hacking tools that were recently stolen, but they didn’t give us signatures to detect their tools. The NSA should take a lesson from FireEye here.
According to the report, “The actors behind this campaign gained access to numerous public and private organizations around the world. They gained access to victims via trojanized updates to SolarWind’s Orion IT monitoring and management software.”
The active campaign likely began in the Spring of 2020 and is considered the work of Russian APT29, aka Cozy Bear.
Multiple signed updates with trojans were hosted on the SolarWinds update site from March-May 2020, including:
hxxps://downloads.solarwinds[.]com/solarwinds/CatalogResources/Core/2019.4/2019.4.5220.20574/SolarWinds-Core-v2019.4.5220-Hotfix5.msp
Once the trojan update is installed, a malicious DLL is loaded by the legitimate SolarWinds.BusinessLayerHost.exe or SolarWinds.BusinessLayerHostx64.exe (depending on system configuration). After sleeping for a random period near two weeks, the malware will resolve a subdomain of avsvmcloud[.]com to find the C2 server.
According to the SolarWinds SEC filing on the issue, SolarWinds believes the number of customers who installed a trojan Orion update to be near 18,000.
The campaign is heavily focused on stealing data, which may be a better alternative to a ransomware campaign. The damage to businesses and the US government from ransom or data loss could have been staggering.
The list of victims includes numerous US agencies, including the US Treasury and Commerce Departments. Krebs on Security has a good analysis on companies using SolarWinds to understand who could be impacted.
It’s unclear if this is the point of initial access, but let’s put on our tinfoil hats and check out a few candidates:
- SolarWinds disclosed in an SEC filing that they are responding to an M365 email compromise that may have allowed attackers to pivot into the organization and modify their build system.
- Early in 2020, the SolarWinds RMM, n-Central, had a vulnerability that would allow the theft of admin credentials. Does SolarWinds use n-Central internally?
- Months before the incident, a weak password for SolarWinds FTP was accidentally published to GitHub. A researcher discovered this and proved an attacker could upload malicious updates to the SolarWinds update site.
We believe the M365 email compromise led to additional access or lateral movement within the SolarWinds environment. If you’re not monitoring your M365, you’ll want to start. Microsoft is not responsible for your M365 security.
Orion makes up approximately 45% of SolarWinds total revenue. So, this could have a big impact on SolarWinds’ revenue and stock value. If you had SolarWinds stock and knew about this breach prior to public knowledge, you’d probably want to sell it before everyone else does.
But that’d be insider trading. And that’s a no-no. But, according to reports, this may have happened. SolarWinds outgoing CEO and large investors in SolarWinds sold millions of dollars’ worth of stock in December before this incident was made public. It’s unclear who knew what when, but I’m sure someone is looking into it.
SolarWinds stock is currently down over 20% on the news of the breach.
Mitigation recommendations
SolarWinds recommends all customers immediately upgrade to Orion Platform release 2020.2.1 HF 1, which is currently available via the SolarWinds Customer Portal. In addition, SolarWinds has released additional mitigation and hardening instructions here.
For the love of everything holy, please upgrade. If you’re unable to upgrade, the following are mitigation techniques until you can upgrade. If attacker activity is discovered in an environment, we recommend conducting a comprehensive investigation.
- Isolate SolarWinds servers until an investigation is conducted. This should include blocking all Internet egress from SolarWinds servers.
- If SolarWinds infrastructure isn’t isolated, consider taking the following steps:
- Restrict endpoints from SolarWinds servers, especially your crown jewels.
- Restrict the scope of accounts that have local administrator privileges on SolarWinds servers.
- Change passwords for accounts that have access to SolarWinds servers/infrastructure. Based on further review/investigation, additional remediation measures may be required.
- If SolarWinds is used to manage networking infrastructure, review network device configurations for unexpected/unauthorized modifications.
- Note: This is a proactive measure due to the scope of SolarWinds functionality, not based on investigative findings.
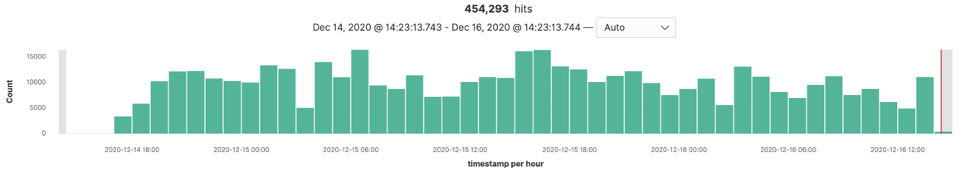
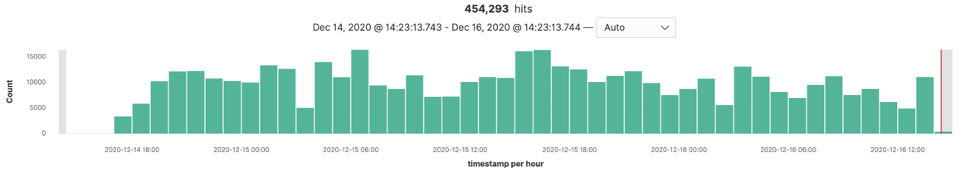
Flock vision
As soon as we read FireEye’s report, Perch deployed the FireEye signatures for all customers. Additionally, we began hunting backward through available customer data looking for matches on hashes, IPs, domains, and relevant logs. We found twelve customers showing signs of SunBurst infection. Two admitted they were just testing us, but we worked with the rest to confirm infections.
If you’re looking for some Elastic searches you can use to discover SunBurst activity, we’ve got you covered. Perch’s SIEM is powered by Elastic, so these queries will work in both.
If you have your elastic index templates set up correctly in your own elastic, searching for Domain and IP IOCS should be super simple.
("avsvmcloud.com" OR "freescanonline.com" OR "deftsecurity.com" OR "thedoccloud.com" OR "websitetheme.com" OR "highdatabase.com" OR "incomeupdate.com" OR "databasegalore.com" OR "panhardware.com" OR "zupertech.com") OR (3.59.205.66 OR 4.193.127.66 OR 4.215.192.52 OR 4.203.203.23 OR 9.99.115.204 OR 5.252.177.25 OR 5.252.177.21 OR 4.188.205.176 OR 1.89.125.18 OR 7.114.213.199) OR ("53f8dfc65169ccda021b72a62e0c22a4db7c4077f002fa742717d41b3c40f2c7" OR "32519b85c0b422e4656de6e6c41878e95fd95026267daab4215ee59c107d6c77" OR "abe22cf0d78836c3ea072daeaf4c5eeaf9c29b6feb597741651979fc8fbd2417" OR "019085a76ba7126fff22770d71bd901c325fc68ac55aa743327984e89f4b0134" OR "ce77d116a074dab7a22a0fd4f2c1ab475f16eec42e1ded3c0b0aa8211fe858d6" OR "439bcd0a17d53837bc29fb51c0abd9d52a747227f97133f8ad794d9cc0ef191e" OR "a25cadd48d70f6ea0c4a241d99c5241269e6faccb4054e62d16784640f8e53bc" OR "d3c6785e18fba3749fb785bc313cf8346182f532c59172b69adfb31b96a5d0af" OR "292327e5c94afa352cc5a02ca273df543f2020d0e76368ff96c84f4e90778712" OR "c15abaf51e78ca56c0376522d699c978217bf041a3bd3c71d09193efa5717c71")
Easy, right?
If you simply want to see where you’re running Orion, here is a query to find process execution for the .exe that loads the malicious .dll. Make sure these hosts are not running a trojaned version.
event.code:1 AND winlog.event_data.Image:(Solarwinds.BusinessLayer*)
Another opportunity to detect Sunburst in action is based on the Sysmon logs for named pipe creation and connection. Sunburst creates and connects to a statically named pipe.
event.code:(17 OR 18) AND winlog.channel:"Microsoft-Windows-Sysmon/Operational" AND winlog.event_data.PipeName:"583da945-62af-10e8-4902-a8f205c72b2e"
If you’re using Sysmon, you can look for Windows process network connections to the reported IPs:
event.code:3 AND destination.ip: (3.59.205.66 OR 4.193.127.66 OR 4.215.192.52 OR 4.203.203.23 OR 9.99.115.204 OR 5.252.177.25 OR 5.252.177.21 OR 4.188.205.176 OR 1.89.125.18 OR 7.114.213.199) OR destination.domain:("avsvmcloud.com" OR "freescanonline.com" OR "deftsecurity.com" OR "thedoccloud.com" OR "websitetheme.com" OR "highdatabase.com" OR "incomeupdate.com" OR "databasegalore.com" OR "panhardware.com" OR "zupertech.com")
If you have Defender, you can detect some SunBurst activity in Defenders logs, blocking an unsigned binary from loading.
event.code:12 AND winlog.channel:”Microsoft-Windows-Security-Mitigations/KernelMode” AND winlog.event_data.Image:”NetSetupSvc.dll”
The beat agent doesn’t collect this log by default. You’ll need to add the log provider to your winlogbeat configuration YAML and restart the elastic beats agent:
-name: Microsoft-Windows-Security-Mitigations/KernelMode
If you’re using Suricata, you might have DNS records enabled. A query like this will work:
event_type:dns AND (dns.rrname: ("avsvmcloud.com" OR "freescanonline.com" OR "deftsecurity.com" OR "thedoccloud.com" OR "websitetheme.com" OR "highdatabase.com" OR "incomeupdate.com" OR "databasegalore.com" OR "panhardware.com" OR "zupertech.com") OR (3.59.205.66 OR 4.193.127.66 OR 4.215.192.52 OR 4.203.203.23 OR 9.99.115.204 OR 5.252.177.25 OR 5.252.177.21 OR 4.188.205.176 OR 1.89.125.18 OR 7.114.213.199))
We’ve found evidence of SunBurst activity from many log sources like firewall logs, Windows logs, Cisco Umbrella logs, Carbon Black logs, Cisco AMP logs, and more.
If you’d like to see what the Flock sees, reach out to us for a demo.